Round-the-clock managed protection against today’s evasive threats
Patented machine-learning models, unique threat intelligence and a proven track record of effective targeted attack research ensure continuous defense against even the most complex threats
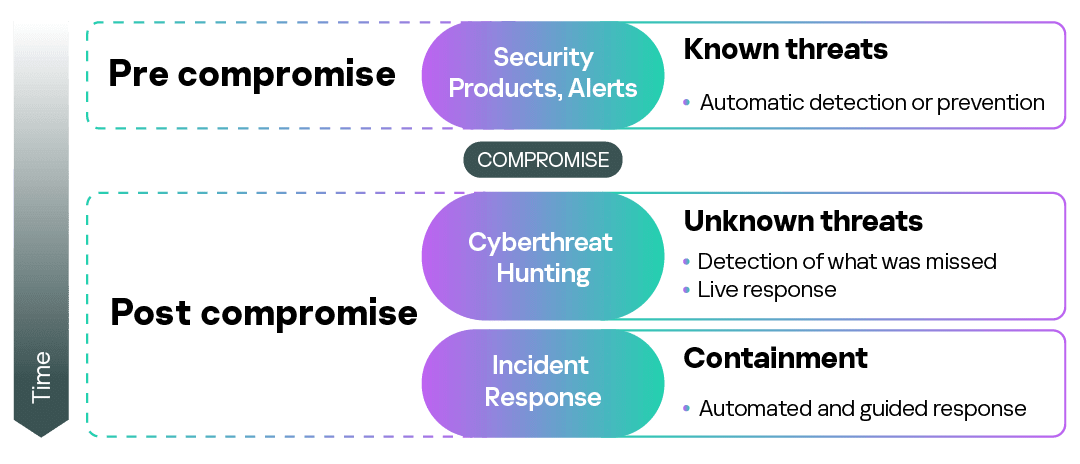
Fully managed and individually tailored ongoing detection, prioritization, investigation and response - preventing business disruption and minimizing the overall impact of any incident
Complete visibility into all observed malicious activities and your existing protection status ensures you have ongoing real-time situational awareness.