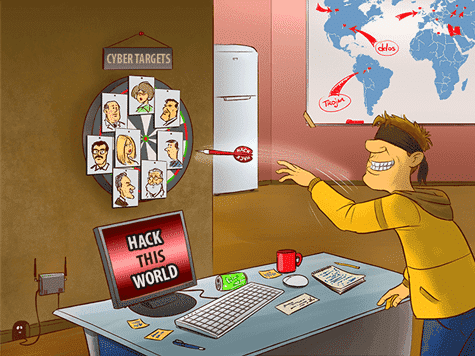
The Internet is truly global—and so are hacking and other cyberthreats. Most foreign hackers are ordinary criminals out for monetary gain, whose exploits range from scams to stealing credit card account data. But “state-sponsored” hacking, by national intelligence agencies, or groups affiliated with such agencies, is a growing concern. Such hackers have access to talent and resources that are far beyond the reach of most ordinary cybercriminals. With their heightened capabilities, foreign hackers pose a powerful threat to government agencies and their employees, as well as individuals or organizations linked to dissidents or other perceived threats. However, they may also target technology or industrial firms in search of innovations they can steal for competitive economic advantage.
When Spies Go Phishing
Intelligence operatives and hacker groups affiliated with them can deploy a wide range of hacking attacks, drawing on the most sophisticated techniques. But some of the most effective espionage hacks may also be among the simplest, such as “phishing.” This is a technique in which an email contains a document or a link to a website that is laden with malware. If the victim clicks on the link, his or her computer becomes infected—not only exposing its data to the hackers, but also allowing the virus to spread through a network.
The hackers may be seeking specific information, but often, the target is just a person. Spies have long sought to compromise and blackmail individuals who might have access to sensitive information. Any private problem—from financial difficulties to a love affair—can provide an opening for such blackmail operations. Phishing and other “social engineering” attack techniques have opened the way to online versions of this ancient espionage ploy.
Here are a few examples of some recent cyberthreats to high-profile organizations that expose the need for better security for companies and individuals.
Sony Hack
2014’s alleged Sony hack really made state-sponsored hacking a lead story. Previous major business hacks have been aimed primarily at retailers, especially their customer credit card data, but the Sony hack was different. The cybercriminals’ primary intention seemed to be to embarrass the firm and its top executives, rather than to steal money. Sony financial information was released along with private emails where executives discussed actors, directors and producers candidly (perhaps a little too candidly). The hack exposed the underbelly of a large corporation and also the film industry, giving the media unprecedented access to previously behind-the-scenes conversations about Sony’s business practices, warts and all.
Hints soon appeared linking the hack to North Korean intelligence operatives. In the murky world of espionage, very little is certain, but as reported at Computerworld some telltale signs eventually emerged, such as a typo in the malware (misspelling the word “security” as “security”) that had previously been noted in hacks tied to North Korea.
University of Virginia Hack
In Summer 2015, the University of Virginia computer network was the site of a new hacking attack tied to foreign intelligence operatives. The university has long-standing ties to the Pentagon and U.S. intelligence agencies, making it a natural target for espionage hacks. As a result, UVA shut down its servers for two days, but reported that no student, faculty, or staff personal information (like Social Security numbers) was compromised.
According to The Hill a newspaper that reports on Congress, the UVA attack apparently concentrated on two specific individual employees “whose work has a connection to China.” And in July, the Pentagon reportedly warned that academic institutions were being hit with an advanced persistent threat by hackers “affiliated with a known foreign intelligence agency.”
Apple Hack
In September 2015, it was discovered that Apple’s App Store had been targeted by Chinese hackers. According to the Wall Street Journal, this is one of the first time Apple’s security has shown vulnerability. Certain Chinese apps, including WeChat, which boasts 500 million active users, were built using an infected version of the XCode developer toolkit that unleashed malware onto mobile devices running the apps, including iPhones and iPads.
It’s not clear what the purpose of this hack was, since it there has not yet been any evidence that information was actually stolen. But Apple joins a growing list of US companies that have been infiltrated by Chinese hackers, including Microsoft and American Airlines. In fact, the FBI warns that any US corporations should be ready for such future attacks.
Most people do not work for government agencies, strategic industries or other organizations that would be obvious targets for foreign hackers working for or affiliated with state intelligence agencies. But you might well know someone who does, perhaps without being aware of the connection, or simply not thinking twice about it. This means that practically anyone can be a potential target of cyberintelligence operations, and find themselves caught up in the shadowy world of espionage.





