Woburn, MA – May 12, 2021 –Kaspersky has released a new report providing a deep look at the ransomware ecosystem. Researchers dug into darknet forums and examined activity by the REvil and Babuk gangs, and others, in an effort to capture the ecosystem’s complexity and debunk some of its myths. The release of the report coincides with the second annual Anti-Ransomware Day, which has been established by Kaspersky and the International Criminal Police Organization (INTERPOL).
Ransomware is a top cyber threat facing businesses in 2021, with criminal groups making daily headlines as they grow bolder. But by placing themselves in the spotlight, those groups obscure the true complexity of the ransomware ecosystem. Kaspersky’s new report seeks to help organizations better understand how that ecosystem operates and how to fight it.
Like any industry, the ransomware ecosystem comprises many players. Contrary to the idea that ransomware groups operate like some kind of modern street gangs, the reality is that a significant number of different actors – such as developers, botmasters, access sellers, ransomware operators – are involved in most attacks, supplying services to each other through dark web marketplaces.
These actors meet on specialized darknet forums where one can find regularly updated ads offering services and partnerships. Prominent big-game players that operate on their own do not frequent such sites. However, well-known groups, such as REvil, that have targeted a growing number of organizations in the past few quarters, publicize their offers and news on a regular basis using affiliate programs. This type of involvement presumes a partnership between the ransomware group operator and the affiliate, with the ransomware operator taking a profit share ranging from 20-40%, while the remaining 60-80% stays with the affiliate.
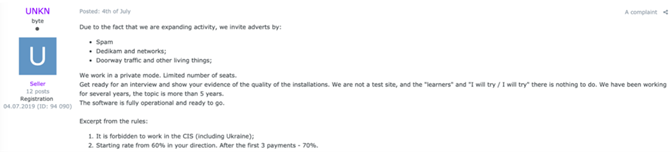
Examples of offers listing payment conditions in the partner programs
Selection of such partners is a finely-tuned process with ground rules set by the ransomware operators from the start, including geographical restrictions and even political views. Meanwhile, ransomware victims are selected opportunistically.
The people who infect organizations and the ones who actually operate ransomware are separate groups, brought together only by the desire to profit. The organizations infected most are often low hanging fruit – essentially, the ones that the attackers were able to gain easier access to. It could be actors within the affiliate programs or independent operators that later sell access – in an auction form or as a fixed price, starting as low as $50. The attackers who create the initial compromise, more often than not, are either botnet owners who work on massive and wide-reaching campaigns and sell access to the victim machines in bulk, or hackers who are constantly on the lookout for publicly disclosed software vulnerabilities to exploit as soon as they are announced and before a patch is applied.
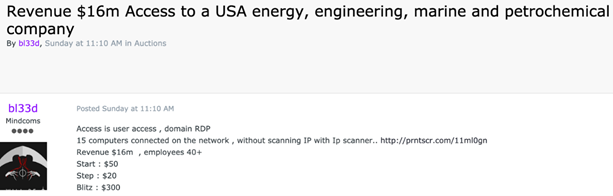
An example of an offer to sell access to an organization’s RDP
Ransomware forums are home to other types of offers too. Some ransomware operators sell malware samples and ransomware builders for anything from $300 to $4,000. Others offer Ransomware-as-a-Service. This is the sale of ransomware with continued support from its developers, which can range from $120 per month to $1,900 per year packages.
“In the past two years, we have seen how cybercriminals have become bolder in using ransomware,” said Craig Jones, Director or Cybercrime, INTERPOL. “Organizations targeted by such attacks are not limited to corporations and governmental organizations – ransomware operators are ready to hit essentially any business regardless of size. It is clear that the ransomware industry per se is a complex one involving many different actors with various roles. To fight them, we need to educate ourselves on how they work and fight them as one. Anti-Ransomware Day is a good opportunity to highlight this need and remind the public of how important it is to adopt effective security practices. INTERPOL’s Global Cybercrime Programme, together with our partners, is determined to reduce the global impact of ransomware and protect communities from harm caused by this growing threat.”
“The ransomware ecosystem is a complex one with many interests at stake,” said Dmitry Galov, security researcher at Kaspersky’s Global Research and Analysis Team. “It is a fluid market with many players, some quite opportunistic, some very professional and advanced. They do not pick specific targets, they may go after any organization – an enterprise or a small business, as long as they can gain access to them. Moreover, their business is flourishing, and it is not going away anytime soon. The good news is that even rather simple security measures can drive the attackers away from organizations, so standard practices such as regular software updates and isolated backups do help and there is much more that organizations can do to secure themselves.”
"Effective actions against the ransomware ecosystem can only be decided once its underpinnings are truly understood,” said Ivan Kwiatkowski, senior security researcher at Kaspersky’s Global Research and Analysis Team. “With this report, we hope to shine a light on the way ransomware attacks are truly organized, so that the community can set up adequate countermeasures.”
Learn more about the ransomware ecosystem in the full report on Securelist.
Register for the free “Darknet and cybergangs: a deep dive into the ransomware ecosystem” webinar, which will take place on May 12 at 10 am EDT: https://kas.pr/vbj1
On May 12, Anti-Ransomware Day, Kaspersky encourages organizations to follow these best practices that help you safeguard your organization against ransomware:
· Always keep software updated on all the devices you use, to prevent attackers from infiltrating your network by exploiting vulnerabilities.
· Focus your defense strategy on detecting lateral movements and data exfiltration to the internet. Pay special attention to the outgoing traffic to detect cybercriminals’ connections. Set up offline backups that intruders cannot tamper with. Make sure you can quickly access them in an emergency when needed.
· Enable ransomware protection for all endpoints. There is a free Kaspersky Anti-Ransomware Tool for Business that shields computers and servers from ransomware and other types of malware, prevent exploits and is compatible with already installed security solutions.
· Install anti-APT and EDR solutions, enabling capabilities for advanced threat discovery and detection, investigation and timely remediation of incidents. Provide your SOC team with access to the latest threat intelligence and regularly upskill them with professional training. All of the above is available within Kaspersky Expert Security framework.
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 240,000 corporate clients protect what matters most to them. Learn more at usa.kaspersky.com.
Media Contact
Sawyer Van Horn
sawyer.vanhorn@Kaspersky.com
(781) 503-1866




