Woburn, MA – March 29, 2021 – In February 2021, Kaspersky detected 1,646 Business Email Compromise (BEC) attacks, a method often used for corporate doxing, according to a report released today. Kaspersky researchers view the attacks as a sign of businesses’ vulnerability to the exploitation of publically available information.
According to the researchers, malicious users have been adopting some of the tricks used by advance persistent threat (APT) groups, such as using ransomware for targeted hits on organizations. In this case, the targeted threat involves corporate doxing; the process of gathering confidential information about an organization and its employees without their agreement, in order to harm them or to profit. Proliferation of publically available information, though data leaks and social media, is making it easier than ever before to trick employees into giving out confidential information or even transferring funds.
Business Email Compromise attacks are targeted attacks in which criminals initiate email chains with employees by impersonating someone from the company. Generally, the purpose of such attacks is to extract confidential information, such as client databases, or to steal funds. Kaspersky researchers analyzed several cases in which criminals impersonated one of the target organizations’ employees using emails very similar to the real ones to extract funds.
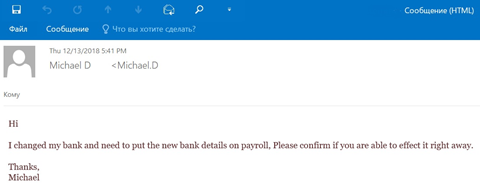
An example of a BEC attack with banking details replacement
Such attacks would not be possible on a massive scale without criminals gathering and analyzing public information available on social media and beyond, such as names and positions of employees, their whereabouts, vacation times and more.
BEC attacks are just one type of attack that exploits publically available information in order to harm an organization. The diversity of ways organizations can be doxed is staggering and, besides the more obvious methods such as phishing or compiling profiles on organizations using data leaks, includes more creative, technology-driven approaches.
Deepfakes are one such approach, provided there is public data to begin with. Doxers simply need some kind of visual image of the target employee and basic personal information. Voices can also be abused. A top-level speaker appearing in a webinar or podcast could potentially end up having their voice recorded and then imitated later, for instance, in a call to accounting requesting an urgent banking transfer or sending over clients’ database.
“While doxing is generally believed to be an issue for regular users – we often see it figure in social media scandals – corporate doxing is a real threat for an organization’s confidential data and one that should not be overlooked,” said Roman Dedenok, security researcher at Kaspersky. “The doxing of organizations, just as of people, may result in financial and reputational losses, and the more sensitive the confidential information extracted is, the higher the harm. At the same time, doxing is one of the threats that could be prevented or at least significantly minimized with strong security procedures within an organization.”
Learn more about the methods doxers use to target organizations on Securelist.
Read about the threat of doxing and where one’s data may end up here.
In order to avoid or minimize the risk of a successful attack on an organization, Kaspersky recommends:
- Establish a rigid rule to never discuss work-related issues in external messengers outside of the official corporate messengers, and train your employees to strictly adhere to this rule.
- Help employees become more knowledgeable and aware of cybersecurity issues. This is the only way to effectively counteract the social engineering techniques that are aggressively used by cybercriminals. To do so, use an online training platform such as Kaspersky Automated Security Awareness Platform.
- Educate employees on basic cyber threats. An employee who is well versed in cybersecurity issues will be able to thwart an attack. For instance, if they receive an e-mail from a colleague requesting information, they will know to first call the colleague to confirm that they actually sent the message.
- Utilize anti-spam and anti-phishing technologies. Kaspersky provides several of these types of solutions, which are included in the following business-oriented products: Kaspersky Security for Microsoft Exchange Servers, Kaspersky Security for Linux Mail Server, Kaspersky Secure Mail Gateway, and the standalone product Kaspersky Security for Microsoft Office 365.
About Kaspersky
Kaspersky is a global cybersecurity company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 250,000 corporate clients protect what matters most to them. Learn more at usa.kaspersky.com.
Media Contact
Sawyer Van Horn
sawyer.vanhorn@Kaspersky.com
(781) 503-1866




