New report from Kaspersky Lab and the University of Oxford Functional Neurosurgery Group explores existing and future risk scenarios impacting implanted devices
Woburn, MA – October 29, 2018 – Researchers from Kaspersky Lab and the University of Oxford Functional Neurosurgery Group have issued a new report, which identifies existing and potential vulnerabilities in implanted brain stimulation devices. As scientists are using these devices to explore how memories are created in the brain and can be targeted, restored and enhanced, these vulnerabilities could be exploited in the future to steal personal information, alter or erase memories or cause physical harm.
For this project, the researchers combined practical and theoretical analysis to explore the current vulnerabilities in implanted devices used for deep brain stimulation. Known as Implantable Pulse Generators (IPGs) or neurostimulators, these devices send electrical impulses to specific targets in the brain for the treatment of disorders such as Parkinson's disease, essential tremor, major depression, and Obsessive–Compulsive Disorder. The latest generation of these implants comes with management software for both clinicians and patients, installed on commercial-grade tablets and smartphones. The connection between them is based on the standard Bluetooth protocol.
The researchers found a number of existing and potential risk scenarios, each of which could be exploited by attackers. These include:
- Exposed connected infrastructure. The researchers found one serious vulnerability and several worrying misconfigurations in an online management platform popular with surgical teams, which could allow an attacker to access sensitive data and treatment procedures.
- Insecure or unencrypted data transfer between the implant, the programming software and any associated networks. This could enable malicious tampering of a patient’s implant, or even tampering of whole groups of implants (and patients) connected to the same infrastructure. Manipulation could result in changed settings, causing pain, paralysis or the theft of private and confidential personal data.
- Design constraints as patient safety takes precedence over device security. For example a medical implant needs to be controlled by physicians in emergency situations, including when a patient is rushed into a hospital far from their home. This precludes use of any password that isn’t widely known among clinicians. Further, it means that by default such implants need to be fitted with a software ‘backdoor.’
- Insecure behavior by medical staff. Devices with patient-critical software were found being left with default passwords, used to browse the internet or with additional apps downloaded onto them.
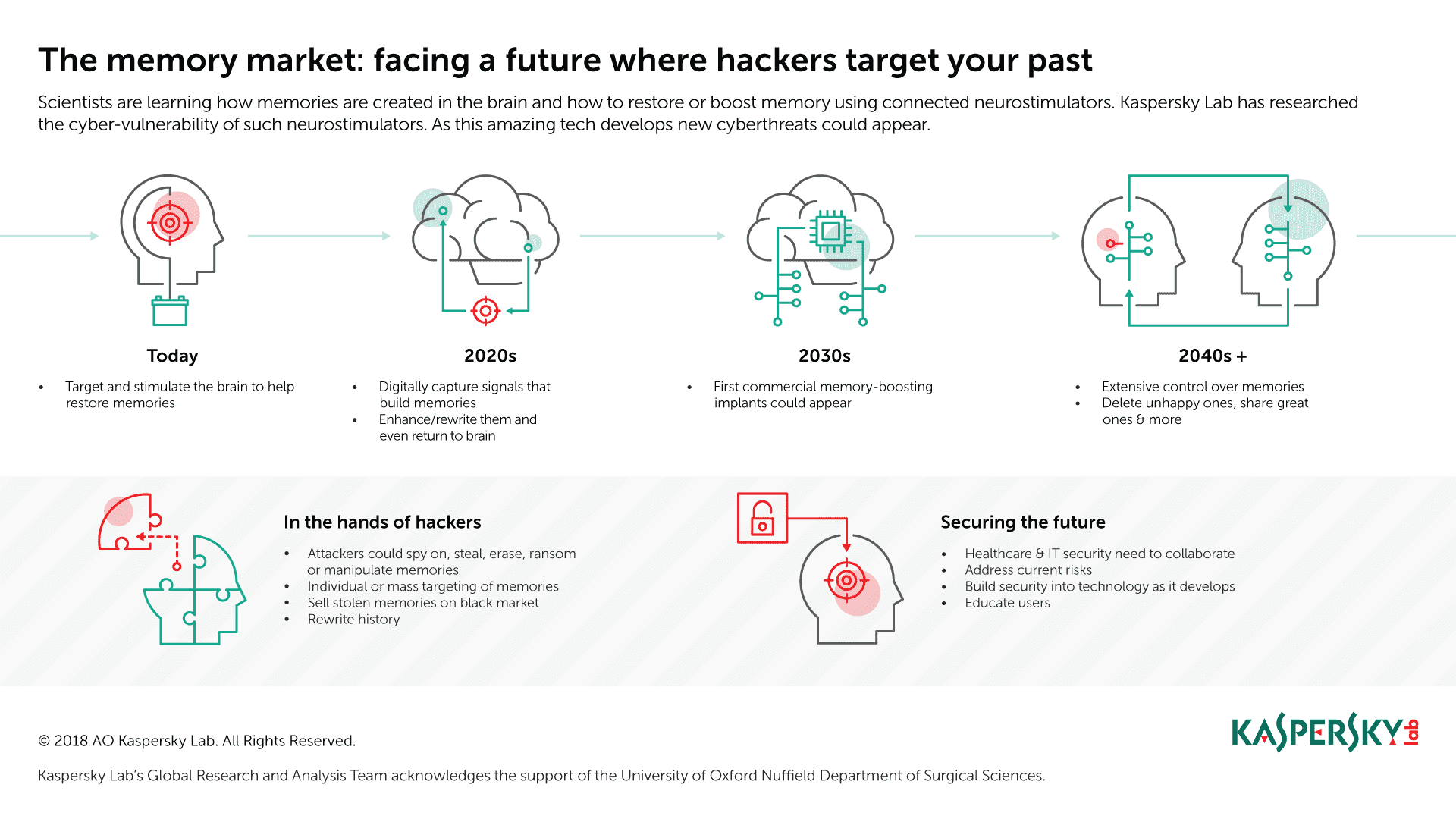
Addressing these vulnerable areas is key, because the researchers estimate that over the coming decades, more advanced neurostimulators and a deeper understanding of how the human brain forms and stores memories will accelerate the development and use of such technology and create in new opportunities for cyberattackers.
Within five years, scientists expect to be able to electronically record the brain signals that build memories, and then enhance or even rewrite them before putting them back into the brain. A decade from now, the first commercial memory boosting implants could appear on the market – and, within 20 years or so, the technology could be advanced enough to allow for extensive control over memories.
New threats resulting from this could include the mass manipulation of groups through implanted or erased memories; while ‘repurposed’ cyberthreats could target new opportunities for cyberespionage or the theft, deletion or ‘locking’ of memories (for example, in return for a ransom).
“Current vulnerabilities matter, because the technology that exists today is the foundation for what will exist in the future,” said Dmitry Galov, junior security researcher, Global Research and Analysis Team, Kaspersky Lab. “Although no attacks targeting neurostimulators have been observed in the wild, points of weakness exist that will not be hard to exploit. We need to bring together healthcare professionals, the cybersecurity industry and manufacturers to investigate and mitigate all potential vulnerabilities, both the ones we see today and the ones that will emerge in the coming years.”
“Memory implants are a real and exciting prospect, offering significant healthcare benefits,” added Laurie Pycroft, doctoral researcher in the University of Oxford Functional Neurosurgery Group. “The prospect of being able to alter and enhance our memories with electrodes may sound like fiction, but it is based on solid science, the foundations of which already exist today. Memory prostheses are only a question of time. Collaborating to understand and address emerging risks and vulnerabilities, and doing so while this technology is still relatively new, will pay off in the future.”
A copy of the report, “The Memory Market: Preparing for a Future Where Cyber-threats Target Your Past” is available on Securelist.
A video showing how memory implant technology could evolve over the coming decades, as well as the associated cyberthreat landscape, can be found here.
About Kaspersky Lab
Kaspersky Lab is a global cybersecurity company which has been operating in the market for over 20 years. Kaspersky Lab’s deep threat intelligence and security expertise is constantly transforming into next generation security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky Lab technologies and we help 270,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
Media Contact
Meghan Rimol
781.503.2671
meghan.rimol@kaspersky.com




